And all three arrived at the same conclusion within the same month.
When three institutions known for running some of the most demanding evaluations in cybersecurity independently reach the same decision, it tells you something about what they found.
Here’s what that process actually involves, and why it matters to any security team evaluating AI SOC platforms today.
Inside a banking security evaluation
Most vendors talk about their product’s capabilities as if it’s the only thing that matters. In banking, it’s the most significant stage, but it can’t happen without clearing several others first.
Here’s what Radiant went through, three times, in three countries: four distinct stages, each one designed to surface the vendors best suited for the job.
Getting shortlisted
Banks don’t evaluate every vendor that reaches out. Before anything begins, internal security teams research the market, compile a long list, and narrow it down based on capabilities, coverage, integration depth, and alignment with their security architecture. Making the shortlist at a bank means you’ve already cleared a bar that eliminates most of the field.
The pre-POC security assessment
Before a bank allows any vendor to access its environment, a preliminary security assessment must be completed. Banks aren’t going to connect an external platform to their security stack without verifying that the vendor meets a baseline security threshold, and this stage alone eliminates vendors before they even deploy in the bank’s environment.
This type of assessment typically includes:
-
- Third-party risks
-
- Security questionnaires like the SIG Lite are tailored to a bank’s specific practices and cover everything from data governance and access controls to incident response and business continuity.
-
- Compliance certifications that have to be current and verifiable
-
- Data residency and privacy reviews that scrutinize where data lives, who can access it, and under what conditions
 Radiant’s privacy and data handling practices were built with this level of rigor in mind: data is hosted in the United States or EMEA, processing is governed by clearly defined lawful bases aligned with GDPR requirements, and we maintain technical, administrative, and organizational security measures that are regularly reviewed and updated to address evolving threats. All of this is foundational to how the platform operates, not something we retrofitted to pass a vendor assessment.
Radiant’s privacy and data handling practices were built with this level of rigor in mind: data is hosted in the United States or EMEA, processing is governed by clearly defined lawful bases aligned with GDPR requirements, and we maintain technical, administrative, and organizational security measures that are regularly reviewed and updated to address evolving threats. All of this is foundational to how the platform operates, not something we retrofitted to pass a vendor assessment.
The technical POC
Only after clearing the security assessment does the real testing begin, not against a curated demo environment, but against the bank’s actual production environment.
Banking security environments operate at a different standard from other industries. These organizations run dozens of security tools across their infrastructure, including endpoint detection, network monitoring, identity management, cloud security, email security, data loss prevention, and more. Each tool generates its own stream of alerts, and on any given day, SOC analysts are dealing with hundreds, if not thousands, of alerts flowing in from across their environment.
And unlike many industries, banks can’t afford to have blind spots. Regulatory frameworks require comprehensive monitoring, coverage, and response. The expectation is full coverage, and the consequences of falling short are tangible, from reputational damage that can take years to recover from, to regulatory action and financial penalties.
A complex security infrastructure with dozens of alert types, endless tools, strict regulatory oversight, and zero room for blind spots is the kind of environment Radiant was built for. Where most AI SOC platforms cover the common alert types, the 6-8 categories that account for a significant portion of the alert volume, Radiant goes further. The uncommon alerts, the cross-domain detections, the multi-signal correlations that span the full breadth of a bank’s security infrastructure are exactly where Radiant’s approach to triage takes over.
Full GRC and contract negotiation
Even after proving the technology works, the process takes a step further. The full GRC review goes beyond the pre-POC security assessment into broader organizational due diligence: can we do business with this company long-term? The GRC team’s job is to find reasons to say no, to protect the institution by verifying every vendor claim, reviewing every policy, and flagging every gap they can find.
And then there are the contracts. Banking contracts run 50-70 pages and are reviewed independently by legal, compliance, and security teams. Every clause around data handling, liability, SLAs, incident response, insurance, and financial terms gets picked apart. This stage alone can take weeks or even months and eliminates vendors who aren’t operationally ready to meet the terms banks require.
Three banks independently put Radiant through every one of these stages, and all three closed within the same 30-day window. For the banks’ buying committees and for us, it was a clear signal that the platform was ready for enterprise financial institutions. These security teams didn’t rush to these decisions. Each bank ran its own full evaluation cycle over months. The fact that they converged on the same answer at roughly the same time suggests what they found.
Why did these banks make the same decision?
When we spoke with the security teams at these three institutions during their evaluations, we kept hearing the same question: What happens with the unknown and complex alerts that hit our SOC? As one security operations director at one of the three banks put it, “If we’re doing automated triage, we’re doing it for the whole stack, not just offloading a handful of alert types.”
During the POCs, that’s exactly where the evaluation focused. Each bank pointed Radiant at the alerts their previous tools couldn’t handle: cross-domain detections spanning multiple systems, unusual signals that don’t match any predefined playbook, and multi-step correlations that analysts would otherwise spend considerable time investigating manually. These account for a significant portion of the daily workload, and they’re exactly the alerts that pose the highest risk.
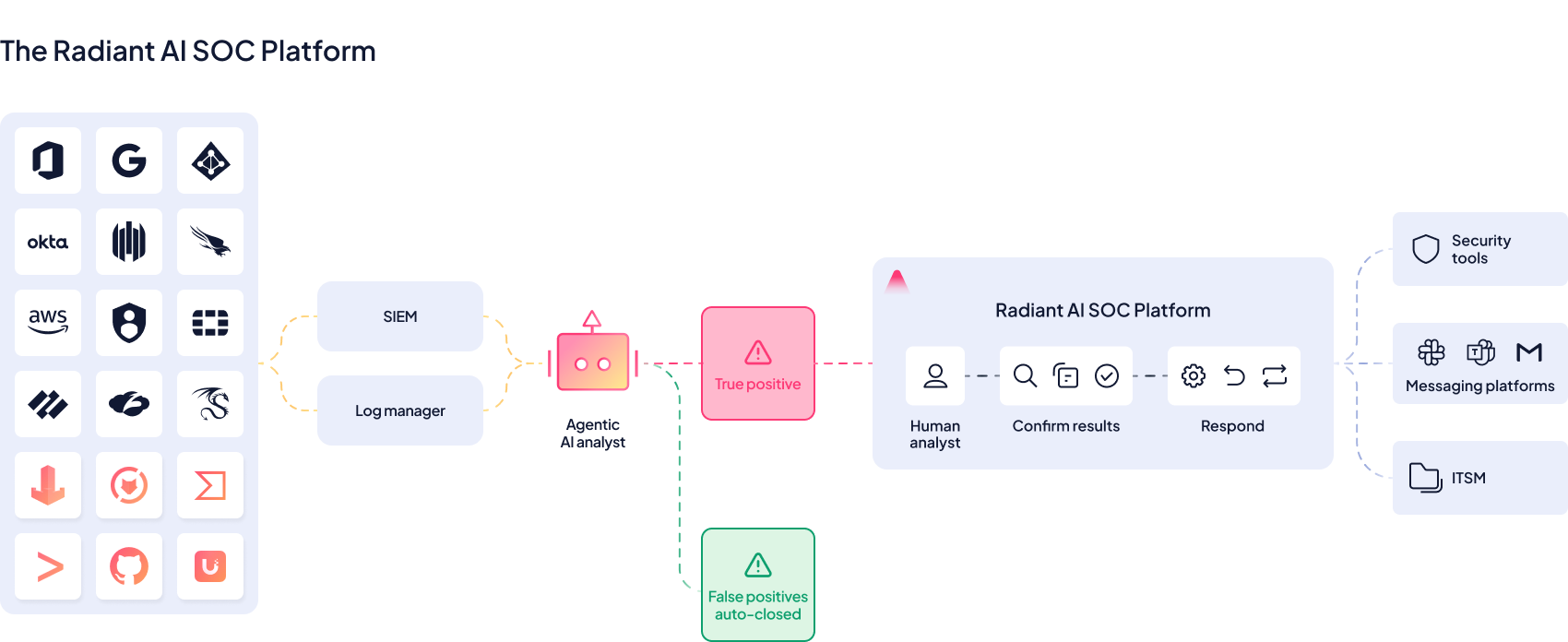
Radiant’s architecture is built for this. The platform integrates with over 120 security tools natively, and its log manager collects, analyzes, and correlates alerts and signals across the entire environment. LLMs are trained to reason like analysts, not just match patterns against a fixed set of alert types, and can investigate and triage alerts that most platforms aren’t built to handle.
Great for banks, great for you.
The banking industry sets the highest bar for vendor security, compliance, and operational rigor. Their GRC requirements are exhaustive. Their security environments are among the most complex, and their tolerance for coverage gaps or operational shortcomings is practically zero.
When a platform consistently clears that bar, it says something about what it can deliver for any enterprise security team. The compliance certifications don’t vary by industry, the data privacy standards don’t relax, and the coverage doesn’t shrink, which means most organizations will find that a platform built to handle banking-grade complexity handles their environment with room to spare.
The approach we’ve taken, building for the hardest environments first, translates into trust with the teams that have the least room for error. If your security environment is complex and your compliance requirements are strict, we’d love to jump on a call and show you what we mean.




