… and how to replicate it with AI and machine learning
In today’s digital age, security breaches have become a significant concern for businesses of all sizes. As a result, the role of security analysts has become increasingly important in building a robust security program. These skilled professionals are responsible for detecting, investigating, and responding to security incidents to protect their organization’s assets and reputation. However, finding and retaining top-notch security analysts has become a significant challenge for many organizations. In fact, many teams (outside of the FAANGs of the world) must settle for candidates that fall well outside their ideal profile because they simply can’t attract the right people.
This blog post will delve into why security analysts are a precious commodity and explore the skills and qualities that make for amazingly effective analysts, and how we might be able to replicate their most important qualities with AI and machine learning.
What Makes Great Analysts Great?
Security analysts are the difference between a quickly remediated incident and a call from the FBI, thus hiring a great team of analysts is of utmost importance. While there are numerous factors that can influence the effectiveness of security analysts in their jobs, three key commonalities amongst all top tier analysts include:
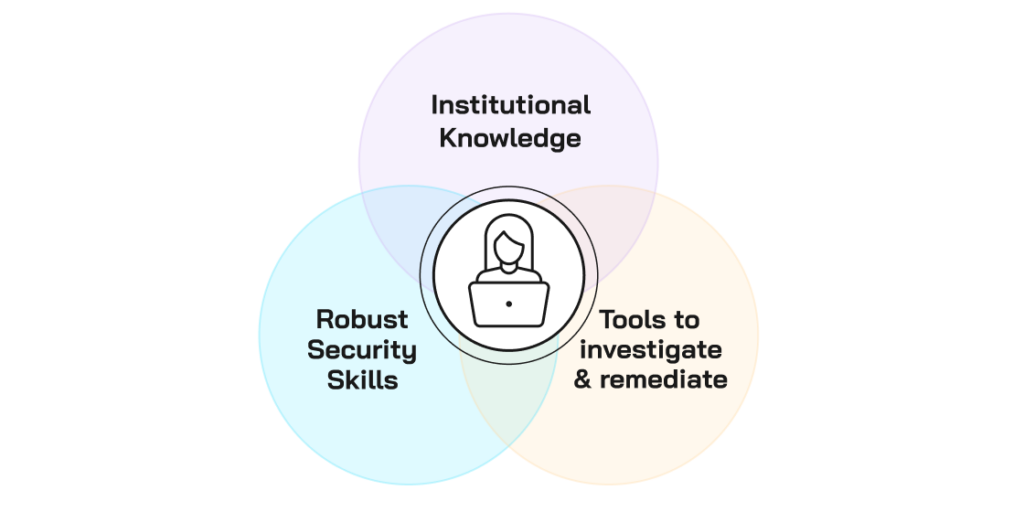
Institutional Knowledge and Learned Context
The value of a great security analyst on any given team cannot be overstated. These professionals have access to a wealth of information (i.e. context) that allows them to perform their duties with precision and effectiveness. This information includes a deep understanding of their organization’s business and IT systems, including what is normal for their environment, users, and business processes. This might include things like knowing who an executive assistant is and that it’s ok for them to access the CEO’s laptop, or who normally accesses the payroll server. Typically this information is gained by time spent within an organization.
Effective security analysts also have a mastery of the security tools that are used as part of their day-to-day activities which makes them efficient in their work. Obtaining this knowledge takes months to years and is one of the reasons why turnover is so painful in this field. When a security analyst leaves, they take this institutional knowledge with them, and new hires take time to build it.
Robust Security Expertise
Similar to institutional knowledge, security expertise is a must for a top-notch security analyst. The best in the biz have a comprehensive knowledge of the security landscape and its emerging threats. They’ve seen it before, either in their current role or elsewhere, and know what to do about it. This enables them to make informed decisions on how to perform triage or an investigation, and then to put together an effective action plan for containment and remediation. This body of knowledge takes years to build and it’s one of the reasons freshly minted analysts are often not as effective as those who have been in the seat for longer periods of time.
Effective Security Tools
Similar to how a carpenter cannot build a house without a hammer, a security analyst cannot effectively perform their job without access to the right tools. It is crucial that security analysts have access to tools that allow them to perform triage, investigation, and remediation of security incidents. However, having access to the right tools is only half the battle. Security analysts must also possess the necessary skills to use these tools effectively to execute their response plan. This requires a combination of technical expertise, problem-solving skills, and a deep understanding of the security landscape. Without the right tools and skills, security analysts are left struggling to keep up with the evolving threat landscape and cannot effectively protect an organization’s critical assets. Great analysts use their skills and access to take appropriate actions to stop the spread of attacks and restore systems back to a healthy state.
How to Replicate these Qualities in Software
The idea of software achieving or surpassing human performance in security operations is an exciting prospect. With advances in machine learning and artificial intelligence, there is potential for software to replicate the nuanced decision-making, intuition, and pattern recognition of human analysts. However, there are certain obstacles that need to be overcome before this can become a reality. Let’s look at how we can overcome these challenges and replicate the necessary human security analyst capabilities.
Implement Continuous Learning
Using AI and machine learning to continually learn about an organization (e.g. locations of employees, OSs, browsers, processes running on machines), the problem space (e.g. new and emerging threats, what they do, and how to respond to them), and past security incidents, closed tickets, and threat patterns is an innovative approach to building the necessary knowledge that takes analysts years to accumulate. This provides the necessary context and a data set for reviewing alerts and incidents with a high degree of accuracy. Such a system can learn faster and more extensively than humans can do it, and the system is constantly updated, which enables it to stay current with emerging threats. By using AI and machine learning, it is possible to replicate the knowledge base that takes analysts years to accumulate and perform security operations more accurately and efficiently.
Create Autonomous Decision-making
Having a wealth of knowledge is not sufficient for conducting security operations. Great analysts use this knowledge to make informed decisions, to determine if security alerts are benign or malicious, to perform investigations, and to put together action plans for stopping the spread of an incident and restoring systems back to health. For triage and investigation this usually takes the form of an interactive question and answer process that starts with a piece of information (usually first obtained from a security alert) and determines what question and answer would progress an investigation the most. For example, for a phishing email “who received/opened/clicked on a suspected phish”? Or did it have an attachment? Was it malicious? Where do the email’s links go? Are they malicious? etc. Software looking to replicate an analyst also needs to be able to replicate this process to perform effective autonomous triage and investigation.
To be clear, I’m not suggesting building a crazy complex “if-then” logic-based playbook like you’d see in a SOAR (Security Orchestration Automation and Response) product. This is far too static and brittle to replace a human analyst. I’m talking about building a “brain” capable of evaluating the information available, selecting and answering the appropriate questions needed to progress triage and investigation efforts and using information from that to repeat the process as needed.
The knowledge base referenced above is one place this decision-making engine gets its answers, along with industry knowledge-bases like threat intel feeds and MITRE ATT&CK. The output of this process is a “blast radius” (i.e. the affected systems, identities, data objects, applications and more) and a root cause analysis which the decision-making engine then transforms into a customized containment and remediation plan that outlines how to address this incident using the organization’s tools.
Utilize Integrations & Automation
The use of API-based integrations to perform automated corrective action is nothing new; it’s a common capability of SIEMs, SOARs, XDRs, and a bunch of other security tools. What is new, is using it in conjunction with the aforementioned decision-making engine and the incident specific response action plan it generates. Think back to our analyst example where we talked about how great analysts combine security expertise and institutional knowledge when containing and remediating incidents. Armed with a similarly deep understanding of the incident, all its affected systems, and the security and IT tools involved, automation has the opportunity to be more surgically and effectively utilized.
Autonomous Security Operations
Radiant Security’s autonomous SecOps platform is leading the way in transforming the security operations space by incorporating AI and machine learning. By automating tasks such as triage, investigation, containment, and response, Radiant Security’s solution eliminates the need for tedious, time-consuming work, freeing up security analysts to focus on higher-level tasks. This not only increases productivity but also boosts analyst retention, morale, and fosters skill development. Radiant Security is at the forefront of leveraging the power of AI and ML to revolutionize the SOC and provide cutting-edge security solutions to its clients.
What to learn more?
Visit us at radiantsecurity.ai to see a demo or learn how autonomous security operations can transform your SecOps program.




