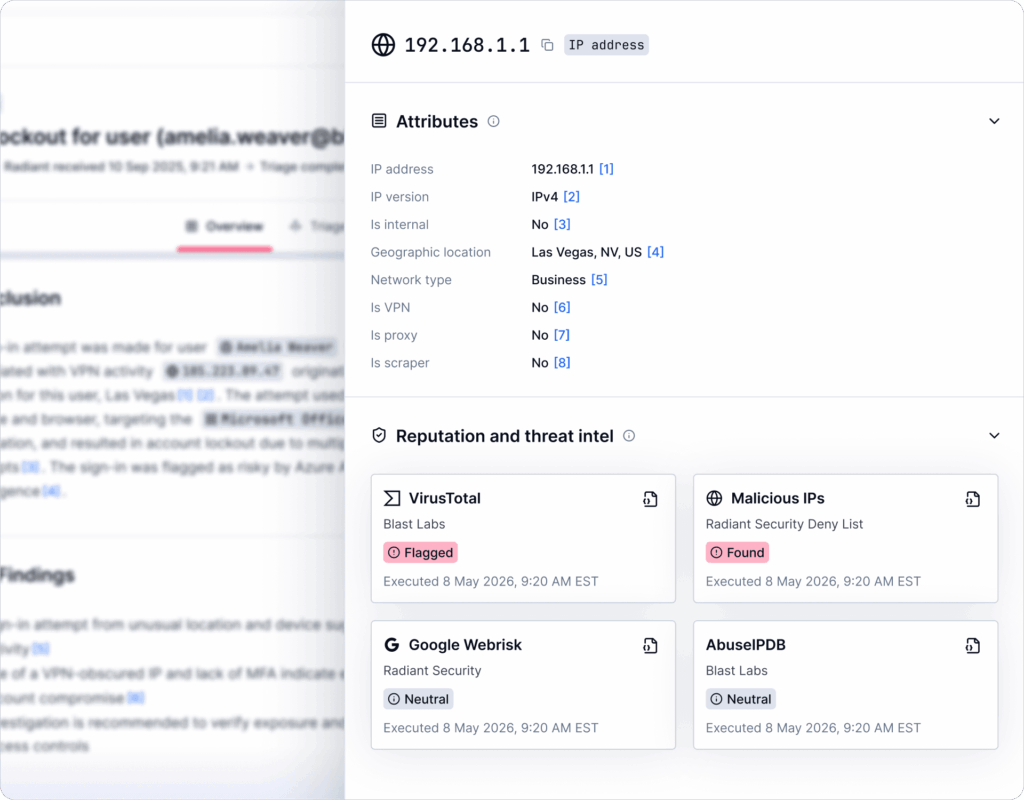
Radiant’s TIS Hub eliminates that pivot. Every artifact encountered during triage is automatically enriched against a curated stack of commercial threat intelligence sources, so the context is already there when you open the alert.
This guide covers Radiant’s TIS Hub: what it is, what’s included out of the box, and how you can get the most out of it.
What is the TIS Hub?
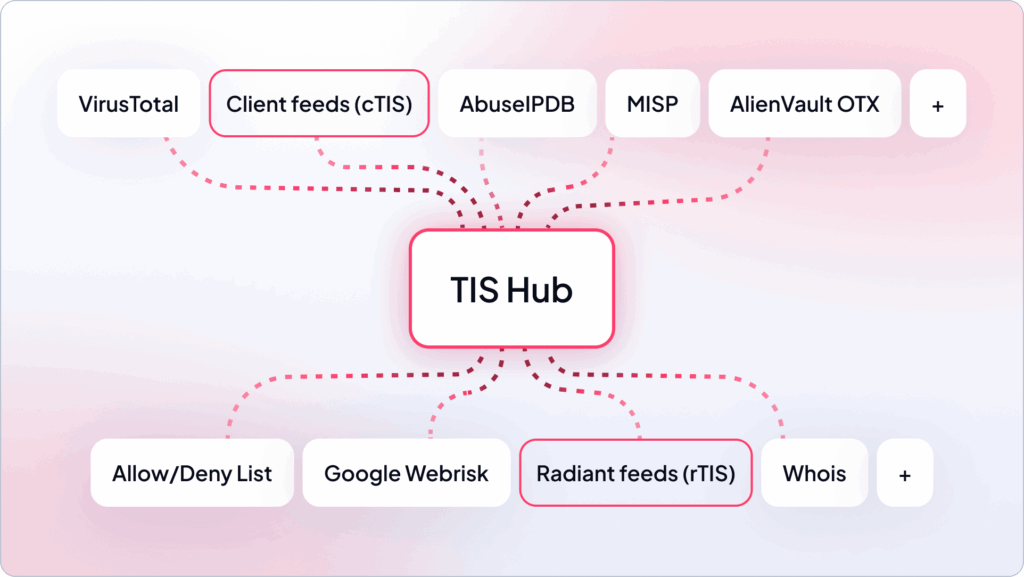
The TIS hub is a unified enrichment layer for threat intelligence, combining two TIS layers:
- Radiant’s TIS (rTIS) — a curated set of built-in commercial threat intelligence sources that Radiant subscribes to, queries automatically on every alert, and makes available to every customer at no extra cost. This is the baseline of the threat intelligence hub.
- Client TIS (cTIS) — a new capability that lets teams connect their own threat intelligence subscriptions directly into the same enrichment pipeline.
If you don’t have your own TIS
For clients who don’t have their own TIS, Radiant covers that for them. Radiant’s built-in TIS give every customer access to a broad stack of commercial threat intelligence sources from day one, with no configuration, no credentials to manage. Radiant feeds are available at no extra cost to all clients and are automatically used for every alert investigation.
These built-in TIS were recently expanded to include new commercial sources, including Perplexity, and now cover nine different TIS.
For teams that don’t hold their own TIS subscriptions, this is your enrichment stack, fully managed, always on, and continuously expanded as Radiant adds new commercial sources.
If you have your own TIS
If your team already holds subscriptions to services like VirusTotal Premium, AbuseIPDB, or internal IOC lists, cTIS (client’s TIS) lets you connect them directly into Radiant’s enrichment pipeline so they’re queried automatically alongside the built-in stack on every triage, so you benefit both from Radiant’s and your unique intelligence layer. Radiant currently supports cTIS for:
- VirusTotal- File hash analysis across 70+ AV engines, URL/domain/IP reputation, malware attribution, sandbox results.
- AbuseIPDB- Community-reported IP abuse history: scanning, brute force, spam, DDoS, exploit sources.
From that point, every triage automatically includes your feeds. No configuration needed.
If you have both
Radiant’s built-in rTIS continue to enrich every alert, alongside one or more of your own cTIS layers, as premium or proprietary intelligence on top. The TIS hub treats both as part of the same enrichment pass: all sources are queried in parallel, and all results surface together in the artifact panel.
Even if you decide to bring your own cTIS, you will continue to benefit from Radiant’s out-of-the-box feeds at no extra cost.
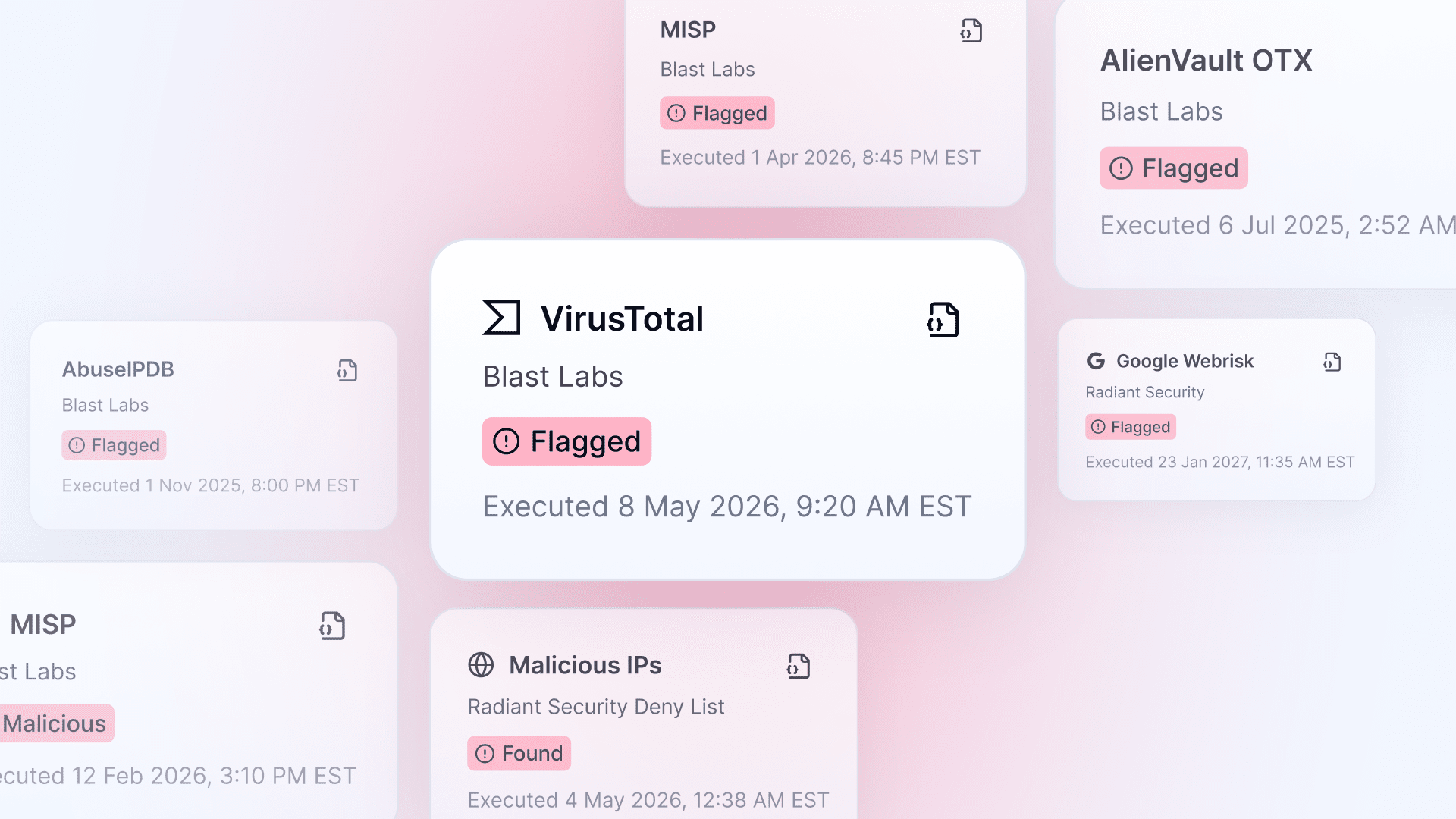
Understanding enrichment attribution
- The provider name and whether the source is Radiant’s TIS (rTIS) or the client’s TIS (cTIS)
- The verdict and timestamp
- A direct link to the provider source report
Getting Started
The TIS Hub is available for all Radiant customers today. Built-in feeds are already running on every alert; nothing is required on your end.
The TIS hub is available for all Radiant customers today. To connect your cTIS
- Go to Settings → Credentials
- Select your provider from the list
- Enter your API key and select your license tier (Public or Premium)
If you’re interested in learning more or seeing Radiant in action, speak to us.