What Are AI SOC Platforms?
AI SOC platforms for autonomous threat investigation in 2026 are shifting from simple, playbook-driven automation to agentic AI systems that can reason, plan, and take action to mitigate threats with minimal human intervention. These platforms are designed to address alert fatigue by autonomously triaging, investigating, and containing threats, allowing security teams to focus on high-value tasks.
Unlike traditional SOCs that rely heavily on human analysts, AI SOC platforms introduce automation at every stage of the incident response lifecycle. This automation allows organizations to scale their security operations, respond to threats faster, and better utilize the expertise of their security teams.
This is part of a series of articles about SOC services
What Is Autonomous Threat Investigation?
Autonomous threat investigation is the automated process of analyzing, correlating, and validating security alerts to determine the nature, scope, and root cause of potential threats without direct human intervention. This capability relies on AI algorithms, behavioral analytics, and contextual data to investigate incidents, prioritize alerts, and produce actionable findings. The goal is to accelerate investigations, reduce dwell time, and enable security teams to focus on issues that require human expertise.
Through continuous learning and adaptation, autonomous threat investigation systems improve their accuracy over time by incorporating analyst feedback and new data sources. These systems correlate disparate events, identify attack chains, and provide clear explanations for their findings to support decision-making.
Features of AI SOC Platforms that Enable Autonomous Threat Investigation
Autonomous Alert Triage
Autonomous alert triage uses AI to prioritize and categorize incoming security alerts based on severity, context, and potential impact. The system evaluates each alert in real time, considering factors such as asset criticality, threat intelligence, and historical data. By filtering out false positives and low-risk events, autonomous triage enables security teams to focus on threats that require immediate action.
This approach learns from analyst feedback and organizational policies, refining its triage models over time. As a result, the system improves at distinguishing between benign and malicious activities, reducing the burden on human analysts. Autonomous alert triage is particularly useful in environments with high alert volumes.
Multi-Agent AI Architecture
Multi-agent AI architecture involves deploying multiple specialized AI agents, each handling specific tasks within the SOC workflow. These agents collaborate, share information, and make independent decisions, allowing the platform to manage complex investigations and responses efficiently. For example, one agent may focus on endpoint analysis, another on network traffic, while a third correlates findings across sources to build a unified threat picture.
By distributing tasks among specialized agents, the system can parallelize processes and adapt to different types of threats. This modular approach improves resilience and scalability, as new agents can be added or existing ones upgraded without disrupting the workflow. Multi-agent architectures support autonomous and coordinated responses to sophisticated attacks.
Autonomous Investigation and Root Cause Analysis
Autonomous investigation capabilities allow the platform to gather evidence, analyze attack paths, and determine the root cause of incidents automatically. The system uses AI-driven correlation and contextual analysis to reconstruct attack timelines, identify affected assets, and map lateral movement within the environment. This accelerates incident investigation and provides findings without manual data gathering or hypothesis testing.
Root cause analysis helps organizations understand how threats bypassed defenses and which vulnerabilities were exploited. By delivering clear findings, the platform supports remediation and informs prevention strategies. Automated root cause analysis also supports compliance reporting and post-incident reviews.
Behavioral Analytics and Anomaly Detection
Behavioral analytics monitors user, device, and network activity to establish baselines of normal behavior and detect deviations that may indicate threats. AI SOC platforms use machine learning models to analyze large volumes of data in real time, identifying anomalies such as unusual login times, data transfers, or access patterns.
These anomalies are flagged for investigation, enabling earlier detection of insider threats, compromised accounts, or advanced persistent threats (APTs). Anomaly detection based on behavioral analytics reduces reliance on static rules and signature-based detection, which are often ineffective against new or sophisticated attacks.
Automated Response and Remediation
Automated response and remediation features allow AI SOC platforms to execute predefined actions in response to detected threats. These actions can include isolating affected endpoints, blocking malicious IP addresses, disabling compromised accounts, or triggering playbooks for remediation workflows. Automation helps contain threats and reduce dwell time.
The platform provides audit trails and logs of automated actions to support compliance and post-incident analysis. By integrating with ticketing systems, IT operations, and other security tools, automated workflows coordinate across teams and systems for remediation. This reduces human error and ensures policy-driven responses to incidents.
AI SOC Platforms for Autonomous Threat Investigation
1. Radiant Security
Radiant Security is an Agentic AI SOC platform that automates alert triage, investigation, and response across the security lifecycle. The platform is designed to reduce false positives by roughly 90%, enabling analysts to spend more time on verified threats rather than manual triage. Radiant also aims to shorten investigation and response times (MTTR) and lower operational costs, while helping teams avoid the fatigue that often comes with high alert volume.
Key capabilities include:
- Agentic AI triage and investigation for all alert types, including previously unseen or low-fidelity ones.
- Transparent reasoning that shows how and why the AI reached its conclusions, helping analysts validate decisions and build trust.
- Integrated response with one-click, executable action plans that can be carried out manually or automated when appropriate.
- Log management with unlimited retention, delivered at a cost significantly lower than traditional SIEM platforms.
- AI feedback loop that allows teams to influence and adjust triage behavior using environmental context, improving accuracy over time.
Radiant provides a unified environment for handling alerts, investigations, response actions, and log data, with an emphasis on efficiency, clarity, and analyst control.
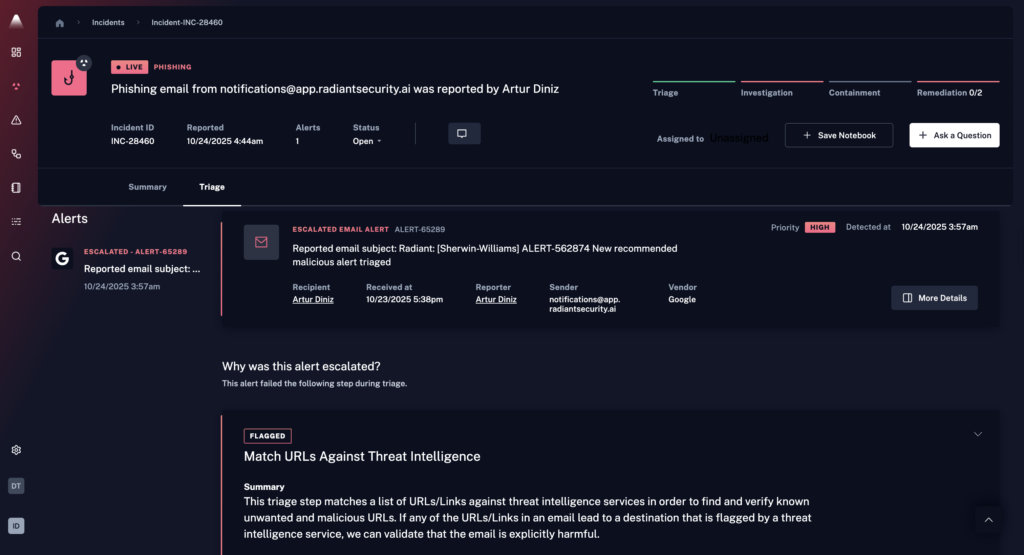
Source: Radiant Security
2. CrowdStrike Charlotte AI
CrowdStrike Charlotte AI is an AI SOC platform built to operationalize an agentic SOC by combining autonomous AI agents with human expertise to accelerate detection and response workflows. It reduces manual effort by embedding AI-driven reasoning across triage, investigation, and orchestration.
General features include:
- AI-driven alert triage: Automatically evaluates incoming detections using threat intelligence, historical patterns, and analyst-trained models.
- Automation of repetitive SOC tasks: Offloads activities such as alert validation, enrichment, and initial investigation steps to AI agents.
- AgentWorks ecosystem for custom agents: Provides a framework to build, test, and deploy AI security agents using natural language inputs.
- Prebuilt and extensible AI agents: Includes ready-to-use agents for common SOC functions, with options for customization.
- Agentic SOAR orchestration: Coordinates actions across tools, agents, and workflows using structured automation and adaptive AI reasoning.
Features relevant for autonomous threat investigation:
- Autonomous alert triage with continuous learning: Uses models trained on analyst decisions to classify and prioritize alerts, improving accuracy over time.
- AI-driven investigation workflows: Conducts multi-step investigations autonomously, gathering evidence and correlating signals.
- Human-guided autonomous reasoning: Allows analysts to steer investigations in real time while the AI continues analysis.
- Dynamic context enrichment: Pulls in relevant data from across the security ecosystem to provide a complete threat view.
- Multi-agent investigation coordination: Uses specialized agents to analyze different aspects of an incident and combine findings.
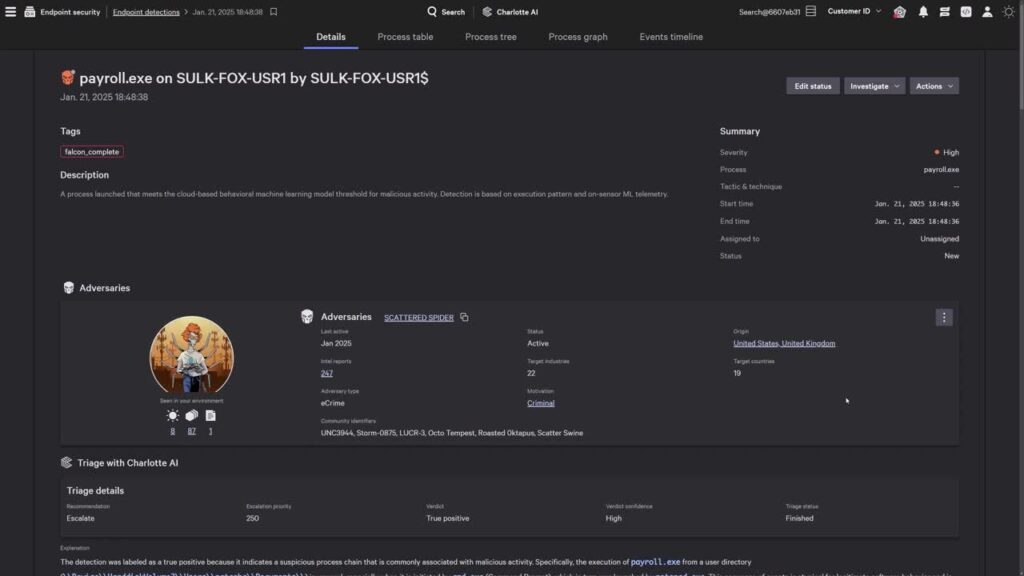
Source: CrowdStrike
3. Google SecOps
Google Security Operations (SecOps) is a cloud-native, AI-powered SOC platform that unifies SIEM, SOAR, and threat intelligence. It uses large-scale data processing and built-in threat intelligence to analyze telemetry and uses generative AI (Gemini) to simplify workflows. The platform provides contextual insights, fast search, and automated response mechanisms.
General features include:
- Cloud-native data ingestion and analytics at scale: Collects and processes large volumes of security telemetry for real-time analysis.
- Integrated threat intelligence: Applies Google threat intelligence to enrich detections.
- Out-of-the-box curated detections: Provides a library of prebuilt detection rules maintained by threat researchers.
- Custom detection engineering with Yara-L: Allows teams to create tailored detections using a query language.
- Generative AI with Gemini: Enables natural language interactions for searching data and creating detections.
Features relevant for autonomous threat investigation:
- AI-assisted investigation with Gemini: Uses a conversational AI assistant to analyze cases, provide context, and generate summaries.
- Automatic entity correlation and alert stitching: Links related alerts, users, devices, and events into a unified view.
- Context-rich alert graphing: Visualizes relationships between entities and events.
- Natural language-driven investigation workflows: Allows analysts to query and refine searches using plain language.
- Real-time access to relevant telemetry: Surfaces additional data during investigations.
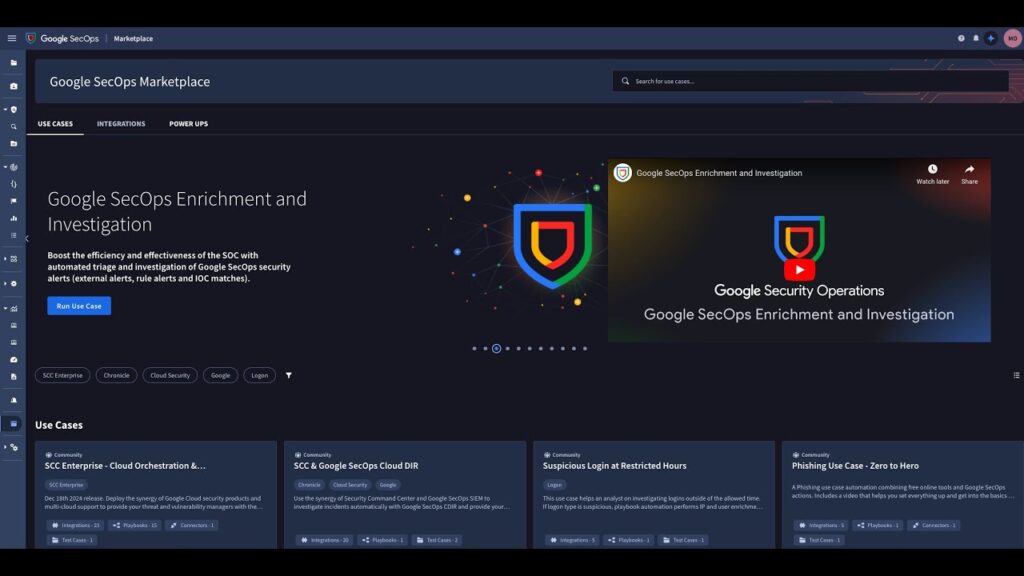
Source: Google SecOps
4. Stellar Cyber
Stellar Cyber is an AI-native security operations platform that unifies detection, investigation, and response across the attack surface. It combines multiple AI techniques, broad data collection, and automated workflows in a single platform. By integrating data from diverse sources and applying multi-layer AI, it improves threat visibility while reducing operational complexity.
General features include:
- AI-native multi-layer detection engine: Combines machine learning and automated threat hunting to identify known and unknown threats.
- Comprehensive attack surface coverage: Monitors activity across endpoints, networks, cloud environments, IoT devices, and servers.
- Flexible data ingestion: Integrates with security, IT, and business tools using prebuilt connectors.
- Sensor-driven data collection: Captures network traffic and log data directly.
- Automated threat hunting capabilities: Enables scheduled threat hunts across the dataset.
Features relevant for autonomous threat investigation:
- Machine learning-based correlation: Links related events into prioritized cases.
- Automated threat hunting workflows: Scans data for suspicious patterns without analyst initiation.
- Guided investigation capabilities: Provides structured investigation paths.
- Contextual data enrichment: Enhances alerts with additional metadata and intelligence.
- Cross-domain visibility and analysis: Correlates activity across network, endpoint, and cloud data.

Source: Stellar Cyber
5. Microsoft Security Copilot
Microsoft Security Copilot is a generative AI-powered security solution that supports SOC operations by providing a natural language interface for investigating and responding to threats. It combines OpenAI models with Microsoft security data, global threat intelligence, and plugin-based integrations to deliver context-aware insights.
General features include:
- Generative AI-powered security assistant: Uses language models to interpret prompts and generate security insights and summaries.
- Natural language interaction model: Allows users to perform tasks such as querying data and investigating incidents without specialized query languages.
- Deep integration with Microsoft security ecosystem: Works with tools like Microsoft Defender XDR, Microsoft Sentinel, Microsoft Intune, and Microsoft Entra.
- Extensible plugin architecture: Integrates with Microsoft and third-party services to pull in alerts, logs, incidents, and policy data.
- Grounded AI responses: Preprocesses inputs with organizational data and threat intelligence before generating outputs.
Features relevant for autonomous threat investigation:
- AI-assisted incident investigation: Analyzes alerts and incidents to produce contextual summaries.
- Natural language-driven threat analysis: Enables users to query telemetry and investigate suspicious activity using prompts.
- Automated alert triage support: Transforms alerts into prioritized insights with recommended next steps.
- Context enrichment through plugins: Aggregates data from multiple sources for investigation.
- Step-by-step remediation guidance: Generates guided response actions to help contain and resolve threats.
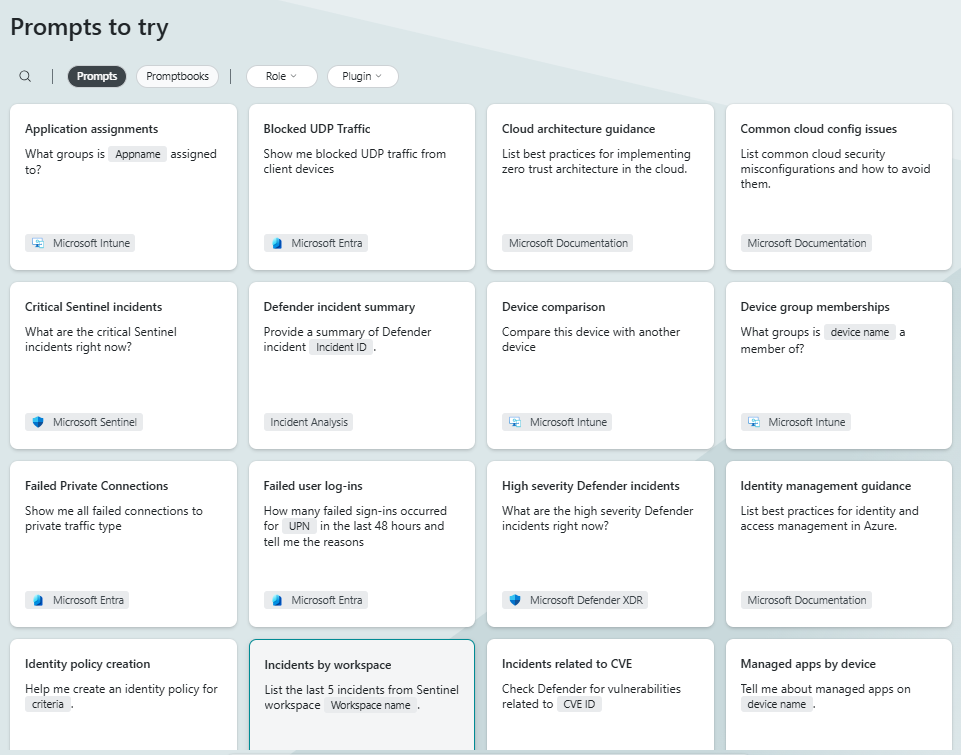
Source: Microsoft Security Copilot
Related content: Read our guide to SOC alerts
Conclusion
AI SOC platforms are redefining how security teams handle investigations by shifting from manual, step-by-step analysis to automated, context-driven workflows. By combining triage, investigation, correlation, and response into a continuous process, these systems reduce alert fatigue and improve response speed. As alert volumes grow and threats become more complex, autonomous investigation becomes essential for maintaining effective and scalable security operations.



