What Are SOC Tools?
SOC tools designed to reduce false positives focus on contextual correlation, AI-driven behavioral analysis, and automated triage to filter noise. These tools, such as Radiant Security, Palo Alto Cortex XSIAM, and Microsoft Sentinel, cut false positives by linking related alerts, learning from analyst feedback, and prioritizing high-fidelity data.
Key techniques SOC tools use to reduce false positives include:
- Contextual correlation: Combining multiple low-confidence alerts into a single high-confidence incident.
- Behavioral baselining: Establishing normal user or network behavior to identify deviations.
- Feedback loops: Incorporating analyst, actions—marking alerts as true or false—back into the system to improve future detection.
- Rule tuning: Regularly refining detection rules to minimize noise.
This is part of a series of articles about SOC services
Benefits of Reducing False Positives in SOC
Reducing false positives in a SOC directly improves how analysts spend their time and how quickly real threats are handled. It shifts effort from noise triage to actual incident response and strengthens overall detection quality.
- Improved analyst efficiency: Analysts spend less time investigating benign alerts. This allows them to focus on real incidents and deeper analysis instead of repetitive validation work.
- Faster incident response: With fewer false alarms, true positives are easier to spot. This reduces detection-to-response time and limits potential damage.
- Reduced alert fatigue: Constant exposure to false alerts leads to fatigue and missed threats. Lowering noise helps analysts stay attentive and make better decisions.
- Higher detection confidence: When alerts are more accurate, analysts trust the system more. This leads to quicker action and less second-guessing.
- Better resource allocation: SOC teams can allocate time and tools toward threat hunting, tuning detections, and improving coverage instead of filtering noise.
- Improved SLA and metrics: Key metrics like mean time to detect (MTTD) and mean time to respond (MTTR) improve when false positives are minimized.
- Enhanced automation effectiveness: Automated workflows and playbooks perform better when triggered by high-confidence alerts, reducing the risk of unnecessary actions.
- Lower operational costs: Less time spent on false alerts reduces staffing pressure and operational overhead, especially in high-volume environments.
- Stronger security posture: Cleaner signal quality leads to better detection tuning and continuous improvement, making the SOC more resilient over time.
What Causes False Positives in SOC Tools?
Poorly Tuned Detection Rules
Detection rules that are too broad or generic often trigger on normal behavior. For example, rules that flag any administrative action or login anomaly without context can generate large volumes of benign alerts.
Lack of regular tuning makes the problem worse. As environments change, rules become outdated and continue to fire on expected activity. Without feedback loops from analysts, these rules fail to evolve and remain a major source of noise.
Misconfigured Data Sources
SOC tools rely on accurate and consistent data ingestion. If log sources are misconfigured, incomplete, or duplicated, they can create misleading signals that trigger false alerts.
Examples include incorrect parsing of log fields, time synchronization issues, or duplicate event collection. These problems distort the data that detection rules depend on, leading to incorrect correlations and unnecessary alerts.
Lack of Contextual Data
Alerts generated without context are harder to validate and more likely to be false positives. For instance, a login from a new location may be legitimate if tied to known user travel, but without that context it appears suspicious.
Missing asset data, user roles, or threat intelligence reduces the ability to prioritize alerts. Enriching events with context such as asset criticality, user behavior, and known indicators helps distinguish real threats from normal activity.
Key Techniques for Reducing False Positives
Contextual Correlation
Contextual correlation combines multiple signals to validate whether an alert represents real malicious activity. Instead of relying on a single event, it links data across logs, identities, assets, and threat intelligence.
For example, a failed login followed by a successful login from the same IP may be benign. But if that IP is tied to known malicious infrastructure and targets a privileged account, the risk increases. Correlation reduces false positives by adding supporting evidence before triggering alerts.
Modern SOC platforms also use rule chaining and event sequencing to improve correlation accuracy. This allows detection logic to account for attack patterns over time, not just isolated events. As a result, alerts become more precise and actionable.
Behavioral Baselining
Behavioral baselining establishes what “normal” looks like for users, systems, and network activity. SOC tools then flag deviations from this baseline instead of relying only on static rules.
For instance, if a user regularly logs in from two locations, that pattern becomes expected. A login from a new country at an unusual time would stand out. Baselining helps reduce noise by filtering expected variations while highlighting meaningful anomalies.
Baselines can be dynamic and adapt over time as behavior changes. Advanced systems use statistical models or machine learning to continuously refine these baselines. This reduces the need for constant manual adjustments while improving detection accuracy.
Feedback Loops
Feedback loops use analyst input to continuously improve detection logic. When analysts mark alerts as false positives or true positives, that data is fed back into the system for tuning.
Over time, patterns of false alerts can be identified and suppressed or refined. This process ensures detections evolve with the environment. Without feedback loops, the same false positives continue to recur and degrade SOC efficiency.
Feedback can also be integrated into automation workflows. For example, SOAR playbooks can update rule conditions or enrichment logic based on analyst decisions. This creates a continuous improvement cycle that strengthens detection quality over time.
Rule Tuning
Rule tuning involves adjusting detection logic to better align with real-world activity. This includes refining thresholds, adding exclusions, and narrowing conditions that trigger alerts.
For example, a rule that flags all administrative actions can be tuned to exclude known service accounts or scheduled tasks. Regular tuning ensures rules remain relevant as systems, users, and attack patterns change. This directly reduces unnecessary alerts while preserving detection coverage.
Effective tuning requires both periodic reviews and data-driven analysis. Metrics such as alert volume, false positive rates, and incident outcomes help identify which rules need adjustment. Consistent tuning keeps the detection stack efficient and aligned with operational needs.
Related content: Read our guide to SOC automation
Notable SOC Tools for Reducing False Positives
1. Radiant Security
Radiant Security is an Agentic AI SOC platform that automates alert triage, investigation, and response across the security lifecycle. The platform is designed to reduce false positives by roughly 90%, enabling analysts to spend more time on verified threats rather than manual triage. Radiant also aims to shorten investigation and response times (MTTR) and lower operational costs, while helping teams avoid the fatigue that often comes with high alert volume.
Key capabilities include:
- Agentic AI triage and investigation for all alert types, including previously unseen or low-fidelity ones.
- Transparent reasoning that shows how and why the AI reached its conclusions, helping analysts validate decisions and build trust.
- Integrated response with one-click, executable action plans that can be carried out manually or automated when appropriate.
- Log management with unlimited retention, delivered at a cost significantly lower than traditional SIEM platforms.
- AI feedback loop that allows teams to influence and adjust triage behavior using environmental context, improving accuracy over time.
Radiant provides a unified environment for handling alerts, investigations, response actions, and log data, with an emphasis on efficiency, clarity, and analyst control.
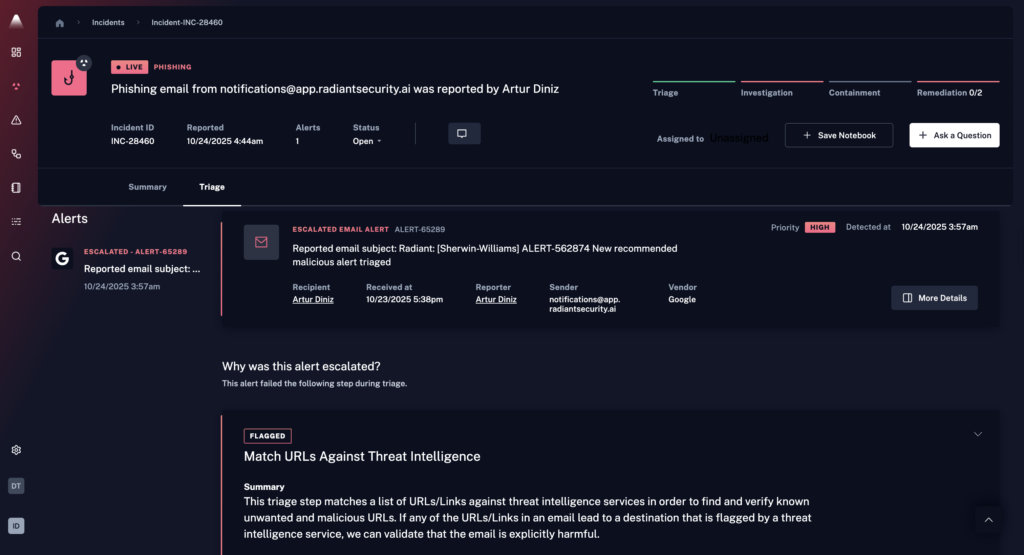
Source: Radiant Security
2. Palo Alto Cortex XSIAM
Cortex XSIAM is an AI-driven SOC platform that unifies SIEM, SOAR, XDR, and attack surface management into a single system built on centralized data, analytics, and automation. It eliminates fragmented tools by consolidating telemetry from endpoints, networks, identity, and cloud, where AI and machine learning models analyze activity and detect threats.
General features include:
- Unified SOC platform: Combines SIEM, SOAR, EDR, NDR, CDR, and attack surface management into a single platform, reducing tool sprawl and operational complexity.
- Centralized data layer (Cortex XDL): Aggregates and processes data from endpoints, network, identity, cloud, and third-party sources into a unified data model for analysis.
- Extensive detection coverage: Provides over 10,000 detections and thousands of analytics and machine learning models to identify known and unknown threats.
- AI-driven analytics and detection: Uses over 2,900 machine learning models to analyze telemetry, detect anomalies, and identify advanced attack patterns.
- MITRE ATT&CK coverage: Maps detections across the MITRE framework to ensure visibility into attacker techniques and coverage gaps.
Features that help reduce false positives:
- AI-based alert reduction: Reduces alert noise by up to 99% by correlating large volumes of signals into a small set of prioritized incidents.
- High-fidelity incident creation: Combines multiple low-level alerts into high-confidence cases with full context, minimizing unnecessary investigations.
- Context-rich alerting: Enriches alerts with data from across endpoints, network, identity, and cloud, improving decision-making and reducing ambiguity.
- Evidence-based vulnerability validation: Attack surface testing validates vulnerabilities by safely simulating real exploits, producing near-zero false positives with proof of exploitability.
- Trusted negative results: Negative findings from exploit testing are reliable enough to close alerts from other tools, reducing duplicate and incorrect findings.
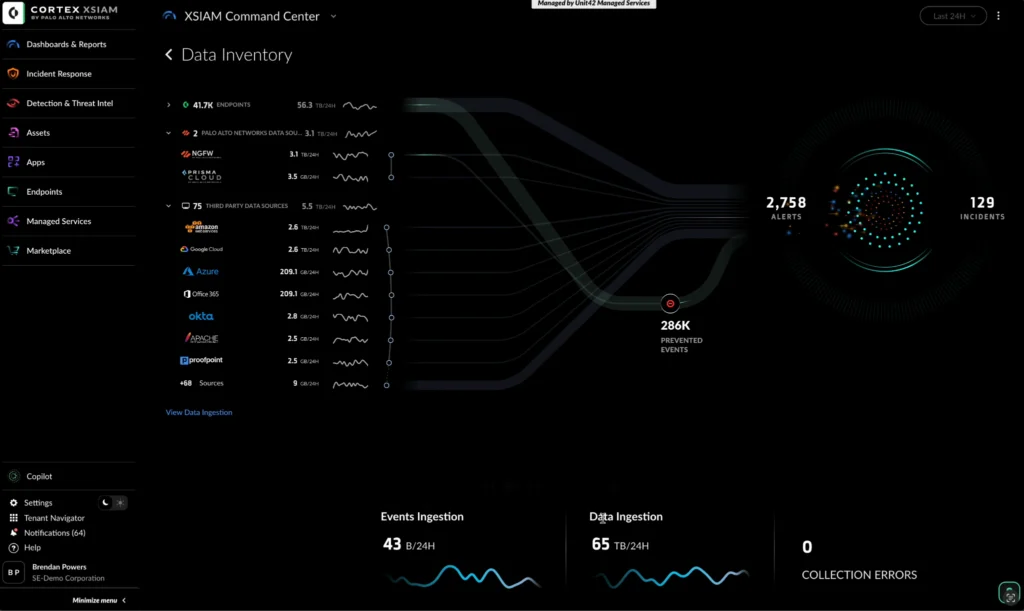
Source: Palo Alto Cortex
3. Microsoft Sentinel
Microsoft Sentinel is a cloud-native SIEM platform that provides centralized visibility across users, devices, applications, and infrastructure. It ingests large volumes of security data from on-premises systems and multiple cloud environments, then normalizes and analyzes that data to detect threats.
General features include:
- Scalable data collection across environments: Collects data from cloud platforms, on-prem systems, applications, and endpoints using built-in connectors, custom connectors, Syslog, REST APIs, and common event formats.
- Out-of-the-box integrations: Includes prebuilt integrations for Microsoft services (such as Entra ID, Azure Activity) and third-party tools, enabling faster onboarding and visibility.
- Data normalization (ASIM): Transforms diverse log formats into a standardized schema at ingestion and query time, improving consistency in detection and analysis.
- Built-in security content: Provides prepackaged SIEM solutions that include detection rules, dashboards, hunting queries, and automation workflows.
- Advanced analytics engine: Uses analytics rules to detect threats, map behavior, and generate alerts based on patterns, anomalies, and known attack techniques.
Features that help reduce false positives:
- Alert grouping into incidents: Combines multiple related alerts into a single incident, reducing duplication and limiting the number of alerts analysts must review.
- Correlation of low-fidelity signals: Connects weak or isolated signals across entities and data sources to form higher-confidence incidents, reducing unnecessary alerts.
- Customizable analytics rules: Allows teams to modify prebuilt rules or create custom ones tailored to their environment, improving detection precision.
- Behavior mapping and anomaly detection: Uses analytics to understand normal activity patterns and flag meaningful deviations, reducing alerts triggered by expected behavior.
- Threat intelligence enrichment: Adds context to detections using known indicators of compromise, helping filter out benign events that lack malicious associations.
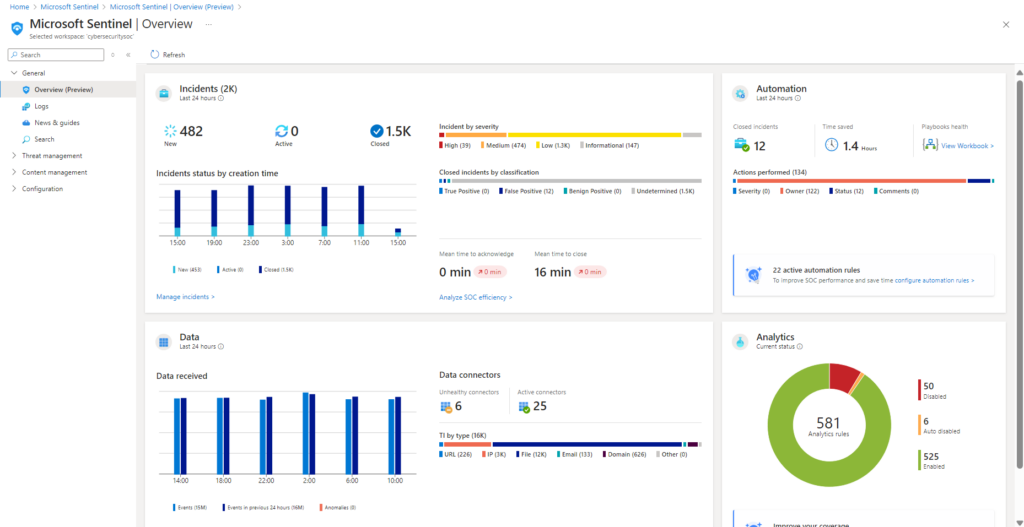
Source: Microsoft Sentine
4. Splunk Enterprise Security
Splunk Enterprise Security is a unified platform for threat detection, investigation, and response that combines SIEM, SOAR, and UEBA capabilities with AI-driven workflows. It centralizes security data from multiple sources and applies analytics, automation, and risk-based prioritization to improve detection accuracy and reduce unnecessary alerts.
General features include:
- Unified TDIR platform: Integrates detection, investigation, and response into a single system to reduce tool fragmentation.
- Full-spectrum visibility: Collects and analyzes data across cloud, endpoints, and on-prem environments for comprehensive monitoring.
- AI-driven workflows: Uses AI to assist with investigations, generate summaries, and automate reporting.
- Detection lifecycle management: Provides tools to build, test, deploy, and monitor detection rules with coverage mapping.
Features that help reduce false positives:
- Risk-based alerting (RBA): Prioritizes alerts based on aggregated risk, increasing true positives and reducing noise.
- UEBA-driven anomaly detection: Uses behavioral analytics and machine learning to detect meaningful deviations.
- Automated enrichment and SOAR: Adds context to alerts and automates response workflows to reduce manual effort.
- High-fidelity alert prioritization: Applies AI to surface the most relevant alerts, lowering overall alert volume.
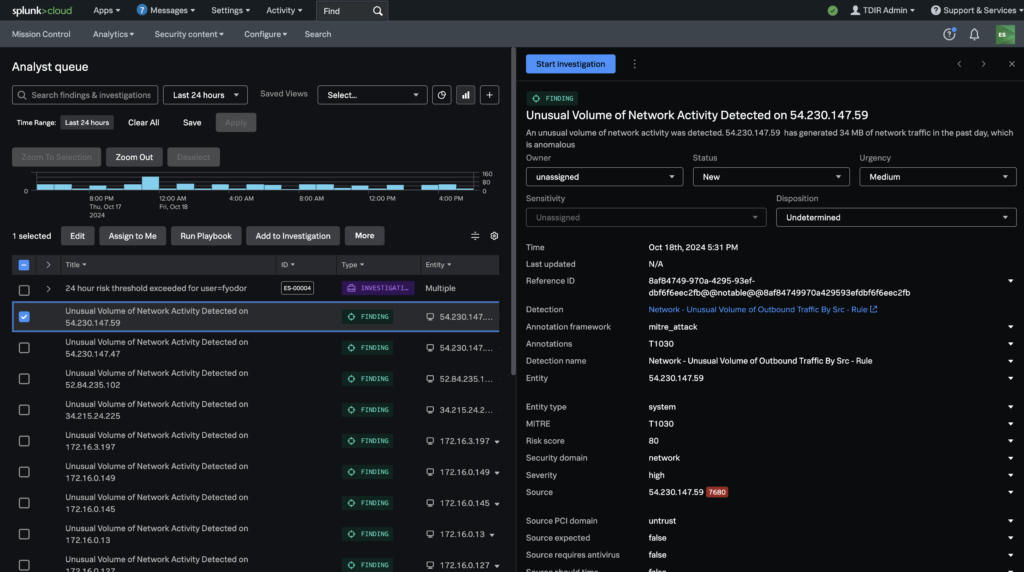
Source: Splunk
5. Sumo Logic Cloud SIEM
Sumo Logic Cloud SIEM is a cloud-native security platform that enables threat detection, investigation, and response using logs-first analytics, behavioral modeling, and automation. It provides centralized visibility across the enterprise by ingesting and normalizing structured and unstructured data, then applying correlation, threat intelligence, and analytics to identify risks.
General features include:
- Cloud-native SIEM architecture: Designed for scalability and elasticity, supporting multi-tenant environments and large-scale data ingestion without infrastructure overhead.
- Real-time data ingestion and analysis: Processes logs and events in real time to detect threats quickly using logs-first intelligence.
- Data parsing and normalization: Converts structured and unstructured data into normalized records, enabling consistent analysis and correlation across sources.
- MITRE ATT&CK coverage explorer: Maps detection rules to MITRE ATT&CK techniques to visualize coverage, identify gaps, and improve detection strategies.
- Advanced threat detection and correlation: Correlates events and signals across the environment to detect both known and unknown threats.
Features that help reduce false positives:
- Signal clustering and insight generation: Automatically groups related alerts into signals and escalates only when combined risk exceeds a threshold, reducing redundant alerts.
- Noise reduction through correlation: Correlates events across normalized data to reduce the volume of raw log events and eliminate isolated, low-value alerts.
- Up to 90% false positive reduction: Built-in analytics and workflows significantly reduce false positives by prioritizing high-confidence insights.
- UEBA-based baselining: Learns normal user and entity behavior quickly, enabling more accurate anomaly detection with fewer false alerts.
- AI-generated context summaries: Summarizes signals within insights to highlight key information, helping analysts avoid reviewing unnecessary raw data.
Source: Sumo Logic
Conclusion
Reducing false positives in a SOC is not a single feature but the result of multiple techniques working together. Contextual correlation, behavioral analysis, feedback loops, and continuous rule tuning all contribute to improving alert quality. When these approaches are applied consistently, they reduce noise, improve analyst focus, and enable faster and more accurate threat response.



