The Radiant Blog
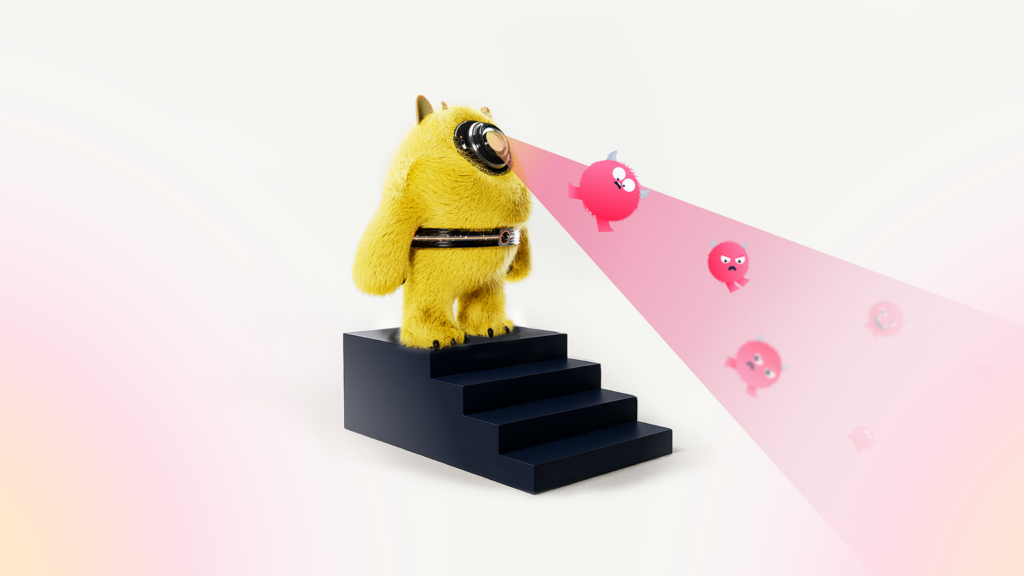
Insights for the modern SOC and actionable thinking for teams that want more from their security stack.
Product Releases
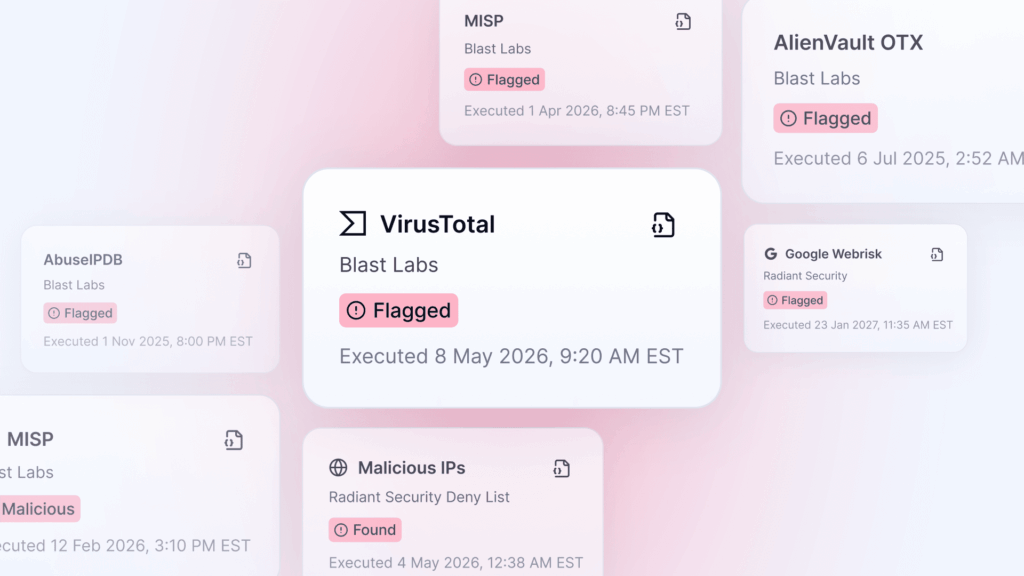
Every investigation hits the same friction point: a suspicious IP or unfamiliar domain that needs context…
All
AI
All Categories
API Security
Business Apps
CDN & Edge
Cloud
Company News
Compliance
CSPM
DLP & Data Security
EDR
Email & Training
Expert Content
Firewalls & Network
IAM
IDS/IPS
Logging & Data Pipeline
MDR
NAC
NDR
OT/ ICS
Product Releases
SASE
SIEM
Supply Chain
SWG & Proxy
Threat Intelligence
VPN & ZTNA
Vulnerability Management
WAF
When your $2M security detection fails: Can your SOC save you?
When your $2M in detection tools inevitably fail, your SOC is the only thing standing between a missed alert and a catastrophic breach. Without a strong last line of defense, you're leaving the door wide open to threats that detection was never actually built to catch.

A practical guide to scaling security operations
Security must scale to protect growing attack surfaces that result from organizational growth.
How to convince the board to level up SOC maturity
Guidance on how to win budget for upgrading your SOC maturity.
The CISO guide to SOC maturity
The SOC is evolving fast, and AI is changing everything. Here’s how to move beyond manual triage and advance your maturity.

Should CISOs be more concerned about employees who use AI or those who don’t?
AI can boost productivity. But it has risks. Learn how to protect your business.

Guidance and tips for a first-time CISO
Discover what it takes to lead with strategy, communicate risk, and build successful teams.

How to advance from SOC manager to CISO?
Making the move from managing a security operations center (SOC) to being a chief information security officer (CISO) is a significant career leap. Not only do you need a solid foundation of tech knowledge but also leadership skills and business smarts. This article will guide you through the practical steps and skills you’ll need to […]

Training high-performance SOC engineers
Explore how to effectively train your SOC engineers, from foundational knowledge to advanced capabilities

Phishing the C-suite: How quick-acting SOC teams caught what everyone else missed
Employees can be a vulnerable entry point and traditional security tools are not infallible. That's why SOC teams should be empowered to focus on what matters.